- A new CloudZ plugin, Phenohijacks Microsoft Phone Link to steal SMS and OTPs from connected Android devices
- This allows attackers to bypass 2FA without compromising the phone itself.
- The RAT retains all of its remote access capabilities, with researchers advocating abandoning SMS authentication.
A new version of the CloudZ Remote Access Trojan (RAT) for Windows now comes with a new plugin that steals data from a connected Android device, experts have revealed.
Cisco Talos security researchers recently spotted the upgraded variant while investigating a breach that has been ongoing since January 2026.
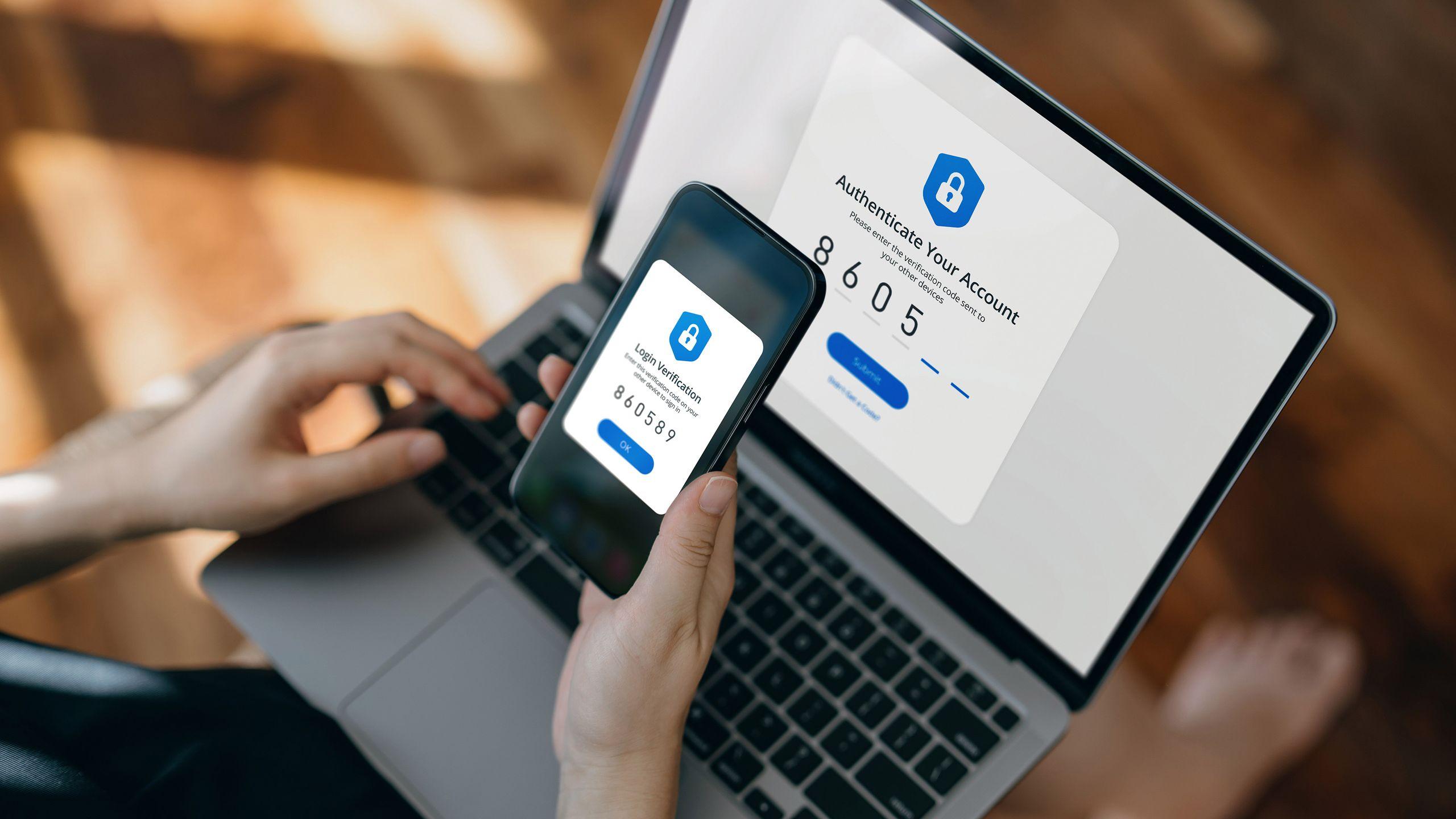
Windows 10 and 11 operating systems have a feature called Microsoft Phone Link, which allows users to connect their Android and iOS mobile devices to their computers. They can then use their computer to take and make calls, text people and more, without having to pick up their smartphone.
Article continues below
Steal 2FA and OTP
While this is certainly a handy feature for replying to WhatsApp and Telegram group messages, it’s even more handy when the device is required for two-factor authentication (2FA). However, this is precisely why CloudZ has been introduced with a new plugin called Pheno.
Which brings us to today.
By hijacking the connection, bad actors can easily exfiltrate not only credentials, but also temporary passwords sent to the mobile device, without having to compromise the phone.
Pheno works by monitoring active Phone Link sessions and accessing the local SQLite database which contains SMS messages and one-time passwords (OTPs).
“With confirmed Phone Link activity on the victim’s machine, the attacker using the CloudZ RAT can potentially intercept the Phone Link application’s SQLite database file on the victim’s machine, potentially compromising SMS-based OTP and other notification messages from the authenticator application,” Cisco Talos said.
Apart from that, CloudZ comes with all the usual RAT features, such as file tampering, running shell commands, screen recording, etc. It attempts to hide its activity by switching between three hard-coded user agent strings, making HTTP traffic appear as legitimate browser requests.
Cisco Talos was unable to determine how victims were infected by CloudZ, but warned that users should avoid SMS-based OTP services and should instead use authenticator apps that do not require interceptable push notifications.
Via BeepComputer
The best antivirus for every budget

Follow TechRadar on Google News And add us as your favorite source to get our news, reviews and expert opinions in your feeds.